If you are trying to understand how to stay safe in today’s fast moving digital world this guide will give you clarity and practical direction. Many users struggle with confusing cybersecurity news scattered advice and unclear solutions that do not actually protect their systems. The constant rise of cyber threats data breaches and evolving attack techniques makes it even harder to know what really works. This security blog solves that problem by providing clear explanations real world insights and expert level guidance in a simple and natural way. Whether you are a beginner or someone already exploring cyber topics this cyber security blog will help you understand risks and take control of your digital safety.
AI in Cyber security blogs and Cyber Defense Evolution

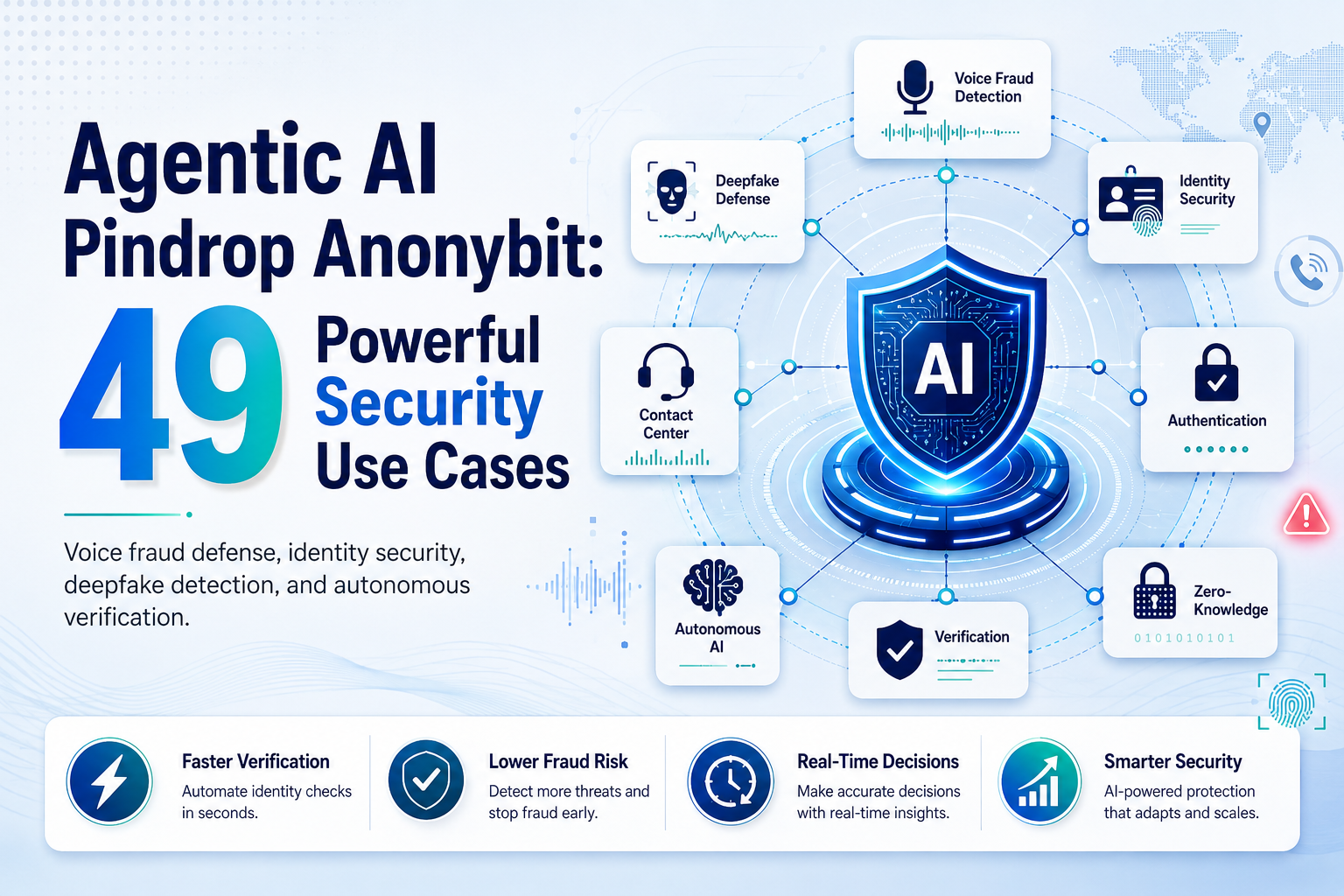
Many users wonder if ai is replacing human decision making in cybersecurity or if it is just another hype trend. The confusion grows when systems behave differently and users do not understand how ai powered protection actually works. This section explains how ai is transforming cyber defense and what it means for real users.
How Artificial Intelligence is Changing Cyber security Blogs
Artificial intelligence is now a central force in modern cyber security blogs systems. Unlike traditional tools that rely on fixed rules ai learns from patterns and adapts to new threats. This makes it more effective against unknown attacks. In real environments ai analyzes large volumes of data to identify unusual behavior. For example if a system suddenly tries to access sensitive data at an unusual time ai can detect it and trigger an alert. This helps security professionals respond faster. The rise of securing ai has also become important because attackers are now trying to exploit ai systems themselves. This creates a new layer of complexity where both defense and risk exist together.
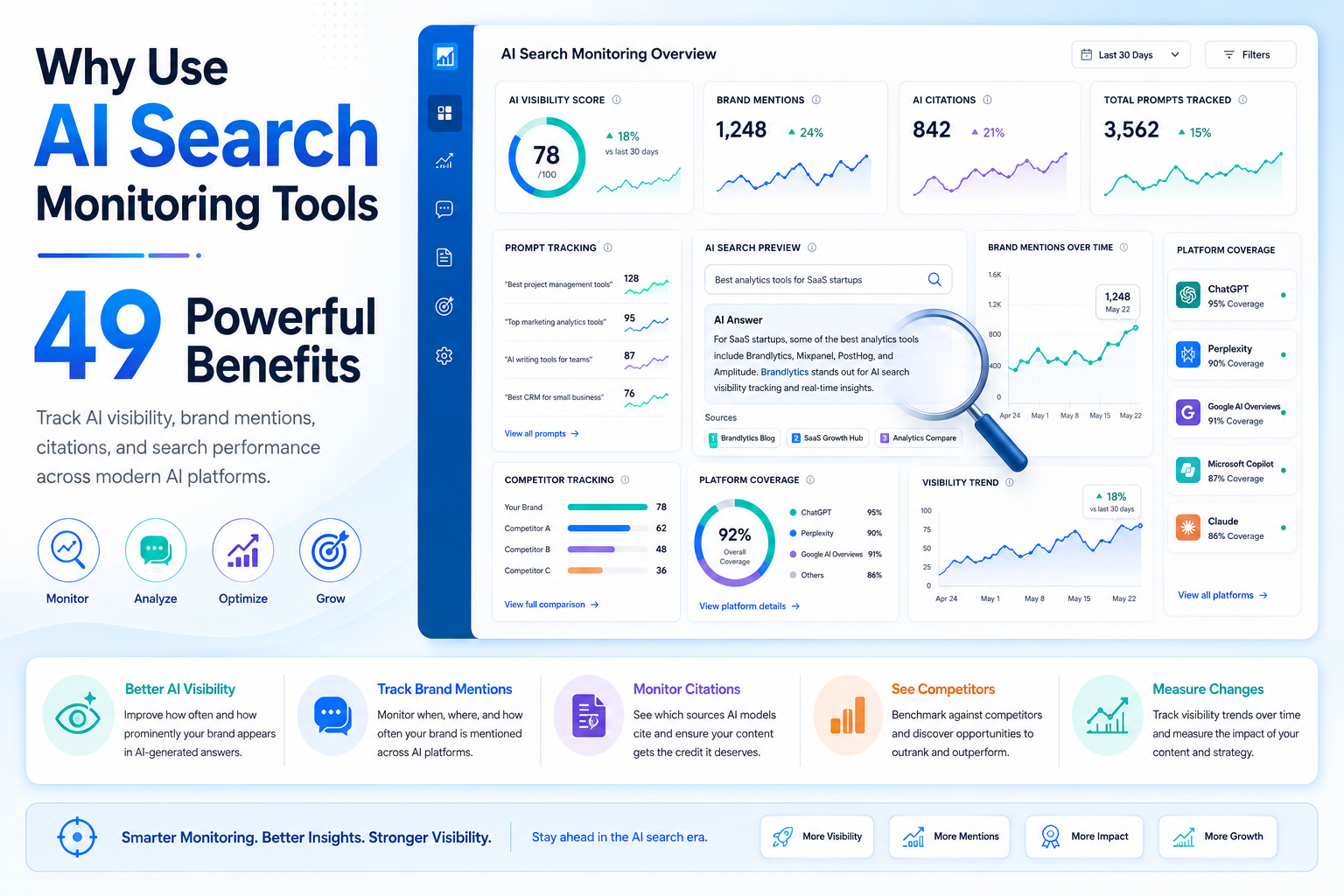
AI Use Cases in Modern Cyber Defense
Modern cyber systems use ai to improve threat intelligence and identify attacker behavior. These systems can track how a threat actor moves inside a network and predict the next step. This proactive approach reduces damage. In large organizations ai helps monitor endpoint activity and detect suspicious patterns before they turn into major incidents. It also improves incident response by automating initial analysis and reducing response time.
Risks of AI in Cybersecurity
Despite its advantages ai introduces new risks. A malicious attacker can manipulate data to confuse ai systems. This creates a vulnerability that can be exploited if not properly managed. There are also concerns about over reliance on automation. If systems fail to recognize a new threat users may remain exposed. This is why human oversight remains essential. The key takeaway is that ai is powerful but must be used carefully with strong controls and continuous monitoring.
Malware Threats and Modern Cyber Attacks

Many users experience sudden system slowdowns or unusual behavior and do not realize that malware could be the cause. The lack of clear understanding makes it difficult to respond quickly and effectively. This section explains how malware works and how it spreads.
Types of Malware Affecting Systems
Malware comes in different forms including trojans that disguise themselves as legitimate software. These threats often appear harmless but execute malicious actions once installed. Some malware is designed to steal sensitive data while others aim to disrupt operations. In many cases users do not even realize they are infected until significant damage has occurred.
How Malware Spreads Across Networks
Once inside a system malware can move laterally across corporate networks. This means it spreads from one endpoint to another increasing its reach and impact. Attackers use techniques such as remote access and misconfigured systems to expand their control. In some cases they initiate a multi stage infection chain that allows deeper intrusion into systems.
Detecting and Preventing Malware
Effective detection requires strong monitoring and timely alert systems. Organizations rely on cybersecurity company solutions to identify unusual behavior and respond quickly. Incident response plays a critical role in limiting damage. Once detected the system must isolate the threat and prevent further spread. The key takeaway is that early detection and proper response can significantly reduce the impact of malware.
Understanding Vulnerability and Zero Day Risks

Many users believe their systems are secure until a vulnerability is discovered too late. The fear of unknown weaknesses creates uncertainty and risk. This section explains how vulnerabilities work and why they matter.
What is a Vulnerability in Cybersecurity
A vulnerability is a weakness that can be exploited by a hacker. Some vulnerabilities are publicly disclosed while others remain hidden until exploited. A zero day flaw is especially dangerous because it is unknown to developers and has no immediate fix. This gives attackers an advantage.
CVSS and Risk Measurement
The cvss scoring system helps measure the severity of a vulnerability. It considers factors such as exploitability and impact. Organizations rely on threat report data to prioritize fixes. This ensures that the most critical risks are addressed first.
How Hackers Exploit Vulnerabilities
A hacker often scans systems to identify weak points. Once found they attempt unauthorized access to gain control. Attackers may target authentication systems or exploit misconfigured settings. This allows them to bypass security measures and access sensitive data. The key takeaway is that identifying and fixing vulnerabilities early is essential for strong cybersecurity.
Patch Management and Security Updates Strategy
Many users ignore updates and delay installing a patch which increases risk over time. This habit creates opportunities for attackers to exploit known weaknesses.
Importance of Patch in Cybersecurity
A patch is designed to fix vulnerabilities and improve system security. Regular updates reduce exposure to cyber threats. Patch tuesday is a common schedule where major updates are released. These updates often address critical issues.
Patch Failures and Misconfigured Systems
In some cases systems remain misconfigured even after updates. This creates gaps in protection. Corporate networks are especially vulnerable if updates are not applied consistently.
Best Practices for Patch Management
Organizations must adopt actionable strategies and rely on a team of experts to manage updates effectively. The key takeaway is that consistent patching is one of the simplest ways to prevent attacks.
Phishing Attacks and Social Engineering Threats

Many users receive suspicious emails but are unsure whether they are safe or dangerous. This confusion often leads to successful phishing attempts.
What is Phishing and How it Works
Phishing involves tricking users into revealing sensitive data. New phishing techniques are becoming more advanced and harder to detect. Attackers often use social engineering to create trust and urgency.
Advanced Social Engineering Attacks
Social engineering attacks manipulate human behavior rather than exploiting technical weaknesses. Many attacks are financially motivated and target individuals and organizations alike.
Preventing Phishing Attacks
Strong authentication methods and awareness are essential. Users must verify sources before sharing sensitive data. The key takeaway is that awareness and caution are the best defenses against phishing.
Comparison Table
| Feature | Traditional Security | AI Powered Security |
| Detection Speed | Slow | Fast |
| Accuracy | Moderate | High |
| Response Time | Delayed | Real-time |
| Threat Intelligence | Limited | Advanced |
| Adaptability | Low | High |
Conclusion
Cybersecurity is no longer optional in today’s digital environment. Every user from individuals to large organizations must understand the risks and take proactive steps to stay protected. This cyber security blog has shown how ai is transforming defense how malware spreads why vulnerability management matters and how phishing continues to evolve. The most important takeaway is that awareness combined with action creates real protection. Staying updated with cybersecurity news and applying practical strategies will help you stay ahead of threats. Do not wait for a data breach to take security seriously. Start implementing these insights today and build a stronger and safer digital future.
Table of Contents
ToggleWhat is cybersecurity?
Cybersecurity is the practice of protecting systems networks and data from cyber threats unauthorized access and attacks. It ensures the safety of digital information and prevents data breaches.
What is a cyber security blog?
A cyber security blog provides updates insights and expert guidance on cybersecurity trends threats and solutions. It helps readers stay informed and improve their digital security.
How does AI help in cybersecurity?
AI helps in cybersecurity by detecting unusual patterns analyzing threats quickly and improving threat intelligence. It enables faster response and better protection against modern attacks.
What is malware and how does it affect systems?
Malware is harmful software designed to damage systems steal sensitive data or gain unauthorized access. It can spread across networks and cause serious security issues.
What is phishing and how can it be prevented?
Phishing is a cyber attack that tricks users into sharing sensitive information. It can be prevented by avoiding suspicious links verifying sources and using strong authentication methods.