If you are looking for a reliable cybersecurity resource that actually helps you stay protected online this guide will give you everything in one place. Many users face confusion when trying to secure their systems because information is scattered and often unclear. This creates frustration and increases exposure to cyber threat risks. The problem is simple. Most users do not know which website to trust or how to apply security in real situations. This leads to weak protection poor decisions and growing vulnerability across digital systems. Without proper guidance even basic computer security fails.
This guide solves that problem by providing a structured cybersecurity resource center approach. You will learn how to use trusted platforms understand risk management and apply actionable strategies to protect sensitive information in a practical way.
Cyber security Resources Center

Cyber security Resources Overview for Security Challenges
Many people struggle to understand cybersecurity because it feels complex and technical. The confusion increases when different sources give conflicting advice. This creates hesitation and delays action which increases cybersecurity risk.
Understanding Cybersecurity in a Digital Environment
Cybersecurity is the process of protecting systems networks and data from cyber threat activity. In a digital environment every device connection and system becomes part of a larger infrastructure that must be secured. A strong cybersecurity approach focuses on prevention detection and response. It ensures that sensitive information remains protected while systems operate safely. Without proper security even small vulnerabilities can lead to serious breaches.
Role of Organization and Professional in Security
Every organization must adopt a cybersecurity program that protects its infrastructure and users. Professionals play a key role by designing systems monitoring threats and improving overall capability. Cybersecurity professionals work across different sectors to ensure that systems remain resilient. Their expertise helps organizations defend against attacks and maintain trust.
Importance of Trusted Resource Platforms
A reliable cybersecurity resource allows users to learn and apply knowledge without confusion. Instead of relying on random sources users should follow structured platforms that provide accurate guidance.
Cyber security Resources Center Platforms to Browse

Many users waste time searching multiple platforms without finding useful information. This creates frustration and slows down learning. A structured resource center solves this problem.
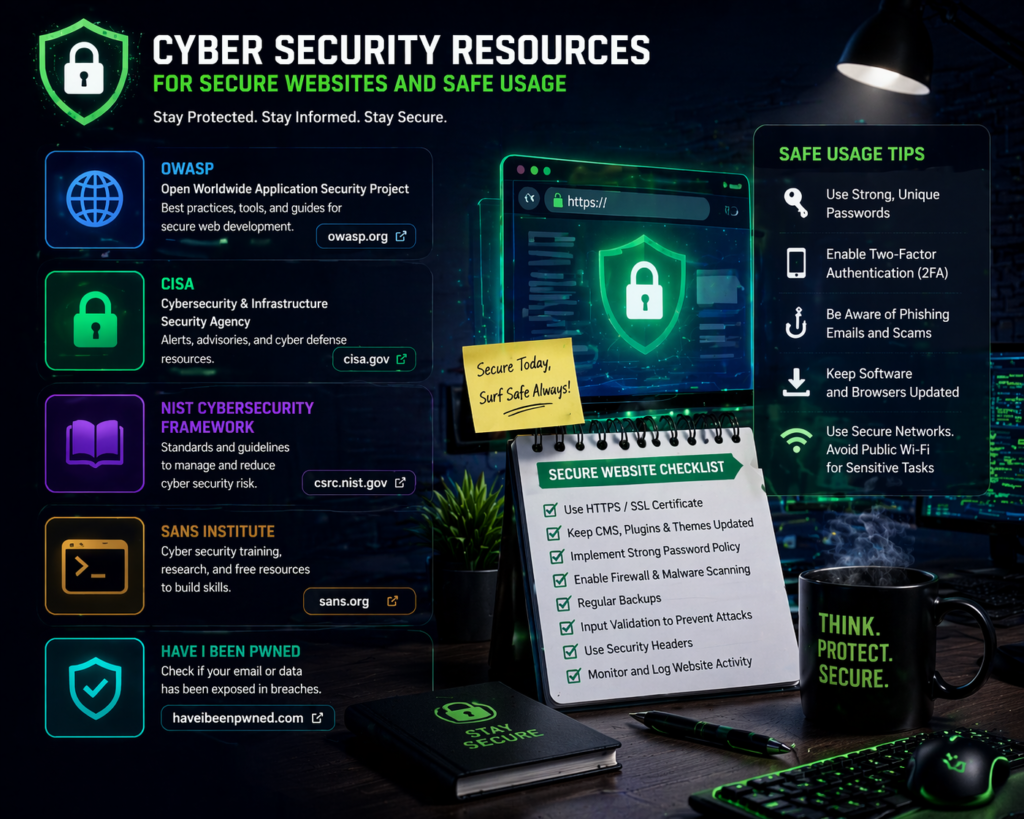
Trusted Platforms like NIST and CISA
NIST provides a well known cyber framework that helps organizations manage risk effectively. The CSF model is widely used and supported by the NCCOE for practical implementation. CISA offers guidance that protects critical infrastructure across the nation. Their gov website provides alerts tools and updates that help users stay informed.
Open Source and GitHub Repository Access
GitHub is a valuable repository where cybersecurity professionals share tools and projects. These open source solutions allow users to explore real world applications and improve their skills. A repository makes it easier to find a cybersecurity tool that matches your needs. It also supports collaboration within the security community.
Free Cybersecurity Platforms and Learning Access
Free cybersecurity platforms help users build knowledge without financial barriers. These platforms often include webinars templates and interactive content. Users can browse a curated list of resources to find relevant information quickly. This improves efficiency and reduces confusion.
Cyber security Resources Template and Practice Guide

Many users understand the basics but struggle to apply them in real situations. Without structured guidance it becomes difficult to build effective protection.
Using Template for Risk Management
A template provides a clear starting point for building a cybersecurity program. It helps users identify threats evaluate vulnerability and create a structured plan. Risk management becomes easier when users follow a proven format. This ensures that no critical area is overlooked.
Hands On Practice and Real World Learning
Practice is essential for understanding cybersecurity. Users must engage in hands on scenarios that simulate real world attacks. Ethical learning environments allow users to explore security concepts safely. This builds confidence and improves practical skills.
Role of Cybersecurity Tool in Implementation
A cybersecurity tool helps automate detection and monitoring. It improves efficiency and ensures that systems remain protected. Tools combined with templates create a strong foundation for managing security.
Security Webinars Podcast and Interactive Learning
Many users find traditional learning methods difficult to follow. This reduces engagement and slows progress. Interactive learning solves this issue.
Webinars and Webinar Based Learning
Webinars provide direct access to industry professionals. They offer insight into real world challenges and solutions. A webinar often includes demonstrations and practical examples that improve understanding.
Podcast and Podcasts for Flexible Learning
A podcast allows users to learn while performing daily activities. Podcasts cover a wide range of topics and provide valuable knowledge in a simple format. This flexibility makes learning more accessible and consistent.
Interactive and Virtual Learning Environment
Interactive platforms allow users to participate actively. Virtual sessions improve engagement and help users develop practical capability.
Repository of Cybersecurity Tool and Open Source Solution
Many users struggle to find reliable tools for their needs. Without guidance they may choose ineffective solutions.
Cybersecurity Tool for Detection and Protection
Detection tools monitor systems and identify suspicious activity. This helps prevent attacks before they cause damage. Penetration testing tools identify vulnerability by simulating real attacks. This improves overall security.
Open Source and AWS Based Solutions
Open source tools provide flexibility and transparency. AWS offers scalable solutions for managing security in cloud environments. These solutions help protect network infrastructure and database systems.
Importance of Organized Repository
A repository organizes tools and resources in one place. This makes it easier to find the right solution.
Cybersecurity Practice for Organization and Professional
Many organizations fail to adopt proper practice which increases risk. This exposes systems to unnecessary threats.
Best Practices for Information Security
Best practices ensure that systems remain protected and efficient. They include strong authentication secure access and regular monitoring. Information security focuses on protecting data from unauthorized access.
Organizational Strategy and Compliance
An organizational approach ensures that security is implemented across all levels. Compliance with standards improves trust and reliability. Medium sized organizations must focus on scalable solutions that fit their needs.
Cybersecurity and Privacy Protection
Cyber security and privacy are closely connected. Protecting sensitive information ensures user trust and system integrity.
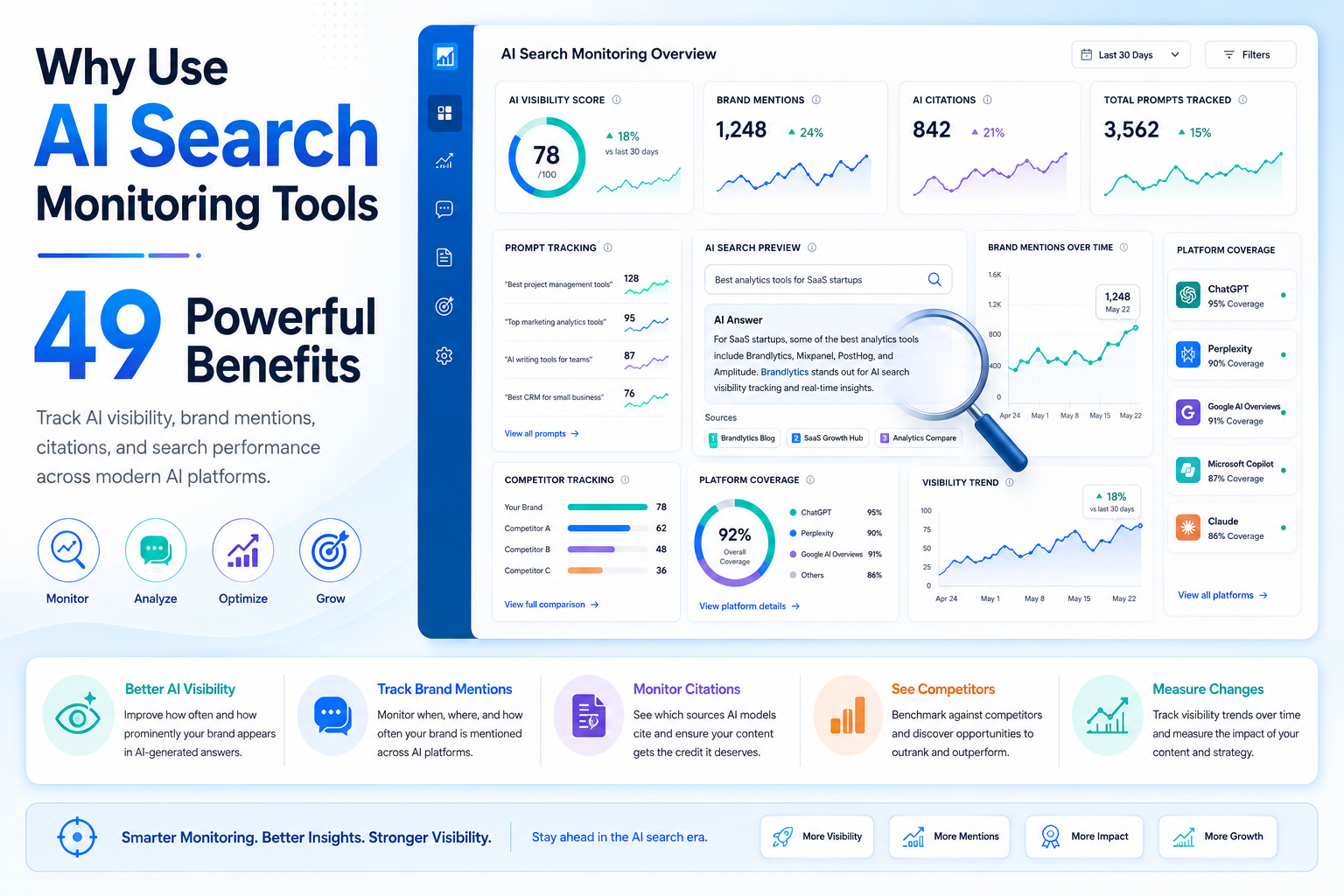
Cyber security Resources for Secure Websites and Safe Usage
Many users access websites without checking if they are secure. This creates unnecessary risk.
Importance of HTTPS and Secure Websites
HTTPS ensures that data is transmitted safely. Secure websites protect users from interception and attacks.
Users should always verify connections before sharing data.
Safe Browsing and Wireless Environment
Wireless networks can expose systems to risk if not secured properly. Users must adopt safe browsing habits to stay protected.
Protecting Sensitive Information
Users must avoid actions that expose data. They should never share sensitive information on untrusted platforms.
Cyber security Resources Center for Critical Infrastructure
Cybersecurity impacts more than individuals. It affects entire sectors and systems.
Protecting Critical Infrastructure
Critical infrastructure must remain resilient against attacks. This includes systems that support essential services.
National Level Security Efforts
Efforts across the nation focus on improving cybersecurity. Organizations work together to defend systems and ensure stability.
Enterprise and Sector Responsibility
Each enterprise must take responsibility for its systems. Strong security ensures long term stability.
Cyber security Resources List of Resources and Certification Path

Many learners do not know where to start. This creates confusion and slows progress.
Curated List of Resources for Learning
A curated list of resources helps users find relevant information quickly. This improves learning efficiency.
Certification and Practitioner Path
Certification provides recognition and builds expertise. A practitioner gains skills through structured learning.
Toolkit and Download Options
Users can download tools and guides to support their learning. A toolkit provides in depth knowledge and actionable steps.
Comparison Table of Cyber security Resources Platforms
| Platform | Type | Capability | Best For |
| NIST | Framework | Risk management and CSF | Organizations |
| CISA | Gov website | Threat alerts and guidance | National security |
| GitHub | Repository | Open source tools | Developers |
| AWS | Cloud platform | Scalable security solutions | Enterprise |
| Free platforms | Learning | Webinars and templates | Beginners |
Conclusion
Cybersecurity is no longer optional. It is a continuous process that requires awareness practice and reliable resources. A structured cybersecurity resource center helps users move from confusion to clarity by providing trusted information tools and guidance. The most important step is to take action. Start by using trusted platforms follow best practices and apply what you learn in real situations. Protect your systems your data and your future by making cyber security a priority today.
Table of Contents
ToggleWhat is a cyber security resources?
A cyber security resources is a platform or website that provides tools guides and information to help users protect systems and data from cyber threats.
Why is cyber security important for everyday users?
Cyber security is important because it protects personal data prevents unauthorized access and reduces the risk of cyber attacks in daily digital activities.
How can I find trusted cyber security resources?
You can find trusted cyber security resources by using official platforms like NIST CISA and verified repositories that provide accurate and updated information.
What are the best practices for cyber security?
Best practices include using strong passwords enabling secure connections updating systems regularly and avoiding sharing sensitive information on unknown platforms.
Can beginners use cyber security tools easily?
Yes beginners can use cyber security tools by starting with simple platforms templates and guided resources that provide step by step learning and practical usage.